Cloaking Hack Puts Spam In Your WordPress Search Engine Results
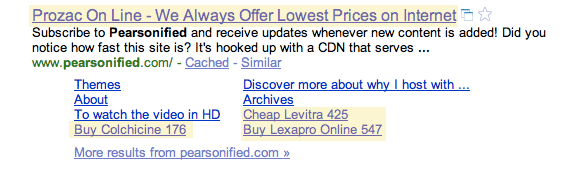
 Since some days a rather nasty hack has been going round in the WordPress community. I actually noticed it myself not that long when I googled for ‘Chris Pearson‘ and what I saw in the results was… shall we say ‘interesting’?
Since some days a rather nasty hack has been going round in the WordPress community. I actually noticed it myself not that long when I googled for ‘Chris Pearson‘ and what I saw in the results was… shall we say ‘interesting’?
Prozac, Levitra, Lexapro? Had Chris sold the ‘Best Damn Blog on the Planet’, AKA Pearsonified? I went to check out Chris’ blog but no. No Prozac, Levitra or anything else of suspicious nature to be found there. Just your regular well-tuned Pearson content. I even looked in the source code and a quick search for known brands ended empty. I left again, having long forgotten already why I googled Chris in the first place.
Now it seems though that this hack is making the rounds and becoming more and more popular. Leland Fiegel from Themelab first reported about it on first reported about it on the Themelab blog, more than a month ago already. Afterwards the issue was covered over at the WP Tavern forums but no solution has been found so far. Even the WordPress Lead Developer, Mark Jaquith, is left clueless and hopes to solve the issue ASAP.
@Skitzzo if someone has actionable security info, they should notify us. If the hackers got in via WP, the access log should have info. [Mark Jaquith on Twitter]
But the hack continues to grow, infecting more and more blogs. On thousands of blogs.
How can you recognise whether your blog is affected?
One option is to wait for Google to cache your content. Did I say before that Yahoo is also targeted with this cloak hack? If I hadn’t so far, I just did.
The other, and faster, way is to use Google’s own Fetch as Googlebot tool. This tool allows you to view how the Google crawlers see your site. Your site must therefor be added to your Google Webmaster Tools account and then you can find it under Labs for every site. In the video below, by Leland Fiegel from Themelab, you can see what the hack does to infected sites.
Read more about the hack at WPBlogger.
Franky is CEO, Editor and 21/7 Muppet on Duty at Splashpress Media. Occasionally he even sleeps. More sporadically even he also blogs about the professional online life at iFranky. He also is regular Guest Lecturer on all things blogging and 'web 2.0'ish'. Follow him on Twitter.

Yeah I got a hack installed on my blog that was promoting the same type of stuff. I have no clue how it got there and I changed my password and everything. It keeps showing up. Do you have any ideas of how to get rid of it?
Much of the time, the hack is already in the template you downloaded or a plugin. The hack is hidden in the code and often upon making changes to the blog – adding post, category, tag, etc – the hack is activated.
Also it may be that it is only revealed when the page is called via a particular user_agent, or only when not logged in (you are often looking at your blog when logged in), etc. or non javascript enabled browser.
You can often detect them by looking for obfuscated code (strange series of characters that are unreadable. There is(was?) a plugin also that will detected encoded/obfuscated code in your wp-content dir (where plugins and themes live).
Hope you get it resolved.
Kevin, it is injected code, so much is clear. Pearson is a well known designer and the hack is still present even when you change the theme. You are right, the injected spam is only visible to search engines (even changing the user_agent might not reveal it).
Garen, right now there does not seem to be a solution but apparently some victims have changed hosting and that solved the problem.
We just found this on our site as well. In our case, something managed to create a malicious file in our blog’s webroot called “temp.php” containing a gzipped, base64 block of code that would look for incoming search engines and re-write the output.
The temp.php file was being loaded from wp-blog-header.php. Deleting the temp.php file and then removing that reference from wp-blog-header.php appears to have cleaned it up for us.
Your site is coming up as the first entry for “wordpress search spam” so I’m hoping this will help some other folks as well.
Please spread the word and stop spam comments.